Transcript below
View Video
Listen to Podcast
Like podcasts? Find our full archive here or anywhere you listen to podcasts: search Community IT Innovators Nonprofit Technology Topics on Apple, Spotify, Google, Stitcher, Pandora, and more. Or ask your smart speaker.
Nonprofit Cybersecurity: Balancing Best Practices, Budget, and Team Productivity
In this webinar co-presented with Build Consulting we answer your questions on nonprofit cybersecurity balancing best practices, including ways to build a cybersecurity budget into your technology roadmap, and create a sound process for managing risks and managing staff training, before you consider the specific cybersecurity technologies available to meet your organizational needs.
Join Build Consulting’s change management expert Peter Mirus and Community IT’s CEO Johan Hammerstrom and cybersecurity guru Matt Eshleman for an in-depth discussion of the competing demands on nonprofit cybersecurity practices – quantifying risks, setting a budget, and guarding productivity.
As with all our webinars, this presentation is appropriate for an audience of varied IT experience. And Build and Community IT are scrupulously vendor-agnostic, so this conversation will feature a realistic look at the cybersecurity tools available – many of them surprisingly affordable, or focused on training and onboarding changes you can make immediately.
You know you need to keep your nonprofit organization safe from cyber criminals. But how safe is safe enough? How much should you budget for the latest defensive technology, and how much should you focus on staff training? How does a nonprofit leader balance cybersecurity and convenience for users? If you make it too difficult to be secure at work, won’t everyone just develop unsafe work-arounds to get their job done?
This webinar is appropriate for nonprofit executives, managers, accounting, development, and nonprofit IT personnel – and as with all our webinars, it is appropriate for a varied audience.
Community IT is proudly vendor-agnostic and our webinars cover a range of topics and discussions. Webinars are never a sales pitch, always a way to share our knowledge with our community.
Presenters:

As the Chief Technology Officer at Community IT and our resident cybersecurity expert, Matthew Eshleman is responsible for shaping Community IT’s strategy around the technology platforms used by organizations to be secure and productive. With a deep background in network infrastructure, he fundamentally understands how technology works and interoperates both in the office and in the cloud.
Matt holds dual degrees in Computer Science and Computer Information Systems at Eastern Mennonite University, and an MBA from the Carey School of Business at Johns Hopkins University.
Matt is a frequent speaker at NTEN events and has presented at the Inside NGO conference, Non-Profit Risk Management Summit and Credit Builders Alliance Symposium. He is also the session designer and trainer for TechSoup’s Digital Security course. He presents updated tips to protect your login credentials throughout the year.
Matt is excited to talk with Peter about nonprofit cybersecurity balancing best practices planning and budgeting, and involving leadership in assessing actual risks and costs.

Peter Mirus co-founded Build Consulting in 2015, following over 15 years of nonprofit consulting experience in the areas of technology, branding, marketing, and development. His work for Build’s clients has a broad focus spanning many operational areas, including fundraising, program monitoring and evaluation, accounting, and impact reporting/analysis.
He presented our recent webinars on creating a technology roadmap, improving data quality and creating an information strategy for your nonprofit, and has been a speaker on nonprofits and technology at Good Tech Fest and NTC.

President and CEO Johan Hammerstrom has always been interested in using technology as a force for good that can improve our world. In college, he pursued this interest through science, first studying Chemistry, Physics and Biology at Stanford University, graduating with Honors with a BS in Chemistry. He then studied Biophysics at Johns Hopkins University and received a Masters Degree.
The time spent in Baltimore convinced Johan that there were more pressing and immediate problems that technology could and should be used to address. He pursued a career in Information Technology, with the express goal of improving our communities and our world. He started at Community IT in 1999 as a Network Administrator. Since that time, Johan has been a Network Engineer, a Team Lead, the Director of Services, Vice President of Services, Chief Operating Officer, and beginning July 2015 President and CEO. Working directly with over 200 nonprofit organizations, to help them plan around and use technology to accomplish their missions, has been one of the most positive and rewarding experiences of his life.
Transcription
Meet the Presenters
Johan: Welcome to the May 2021 Community IT innovators webinar. Thanks for joining us for today’s webinar on Cybersecurity: Balancing Best Practices, Budget, and Team Productivity. Today, we’re going to be talking about a lot of the factors that go into making good cybersecurity decisions and addressing many of the challenges that non-profit organizations face when looking to implement a robust cybersecurity posture.
My name is Johan Hammerstrom, I’m the CEO of Community IT. I’ll be a guest panelist today, and I’m also the moderator for our webinar series. The slides and recording for today’s webinar will be available on our website and our YouTube channel later this week. If you’re watching on YouTube, please consider subscribing to our channel, so that you can receive automatic updates when we post new webinar recordings. We also invite attendees to use the chat feature to ask questions throughout the webinar today and we’ll do our best to respond.
Now, before we begin, I’d like to tell you a little bit more about our company. Community IT is a 100% employee owned company. Our team of 37 staff is dedicated to helping non-profit organizations advance their missions through the effective use of technology. We’re technology experts and we have been consistently named a top 501 Managed Services Provider by Channel Futures, and it’s an honor that we received again in 2020.
I’d also like to start by welcoming our guest, Peter Mirus. Peter, if you don’t mind introducing yourself and then you can tell us a little bit more about Build Consulting.
Peter: Sure. Hi everyone. My name is Peter Mirus, I’m a founding partner at Build Consulting. Build was founded back in 2005 to address the challenge that more than 50% of nonprofits’ technology projects fail, and we primarily focus on business systems, whereas Community IT focuses more on the IT side.
We’re helping you with your broader information strategy, helping you select and implement and assess your needs for ERP, CRM, those different kinds of systems. Like Community IT, we work exclusively with non-profit organizations, and we work collaboratively with our clients to make sure that they are the arbiters of their future. And they’re empowered to make informed choices on their own behalf. I’ve been working in the technology sector for the past 20 plus years, exclusively with nonprofits for the last eight years or so. And I mostly serve as a long-term Information Strategist, helping people create their technology roadmaps and also as a part-time CIO for a wide range of organizations.
Johan: Great. Thank you, Peter, and it’s a pleasure and honor to have you join us today on this webinar. I’d also like to introduce or ask if Matt could introduce himself.
Matt: Sure. Thanks. It’s great to be joining this webinar. We talked last month about our cyber security roadmap and glad to have this opportunity to get Peter’s perspective as a CIO resource to talk about putting these things into practice.
I am the Chief Technology Officer at Community IT. I started as an intern about 21 years ago. So my thoughts today are going back to all those interns who are getting ready to start their own journey and kind of see where it takes them. So, it’s been great to be a part of the team of Community IT. I’m really grateful for this opportunity to talk today.
Johan: Great, welcome back Matt, to the webinar. It’s good to see you. And I’ll just quickly introduce myself as a panelist today. My name is Johan Hammerstrom, I’m the CEO of Community IT. I’ve been with Community IT for just over 21 years. I started off as a technician and have been involved in helping a large number of nonprofits plan and implement technology solutions over the years. And we’ve found that security has become a really essential part of any and every IT discussion, and so we’ve really been focusing on that in our webinar series lately. And we’re really happy to have this conversation today with Peter to talk more about security.
So in terms of what we’re going to be discussing today, we’re going to start with just a basic introduction. The world of cybersecurity is changing rapidly.
It’s changing, I would say on a monthly if not weekly basis, and so it’s always good—we always find it valuable to level set at the beginning of these presentations, just to kind of provide an update on the latest goings on if you will, with cybersecurity.
We’ll talk a little bit more about the
- threat landscape as we see it right now, and then translate that into the
- types of risks that you might be facing as a non-profit organization. What are your specific risks? We’re going to talk about that and that’ll lead into a longer discussion that we’re going to have today around
- how to prioritize cybersecurity. We understand that nonprofits have a lot of constraints. They also have a lot of challenges, a lot of things they need to prioritize.
How do you fit cybersecurity into all of those other things that you have as an organization that you have to work with? That’s going to be the main focus of our conversation today.
So Matt, if you could start by telling us a little bit about what’s going on with cybersecurity right now?
Cybersecurity’s ever changing environment
Matt: Yeah. I mean, it’s a constantly changing and dynamic environment. I think the big takeaway that many organizations are realizing is just how financially motivated these attackers are.
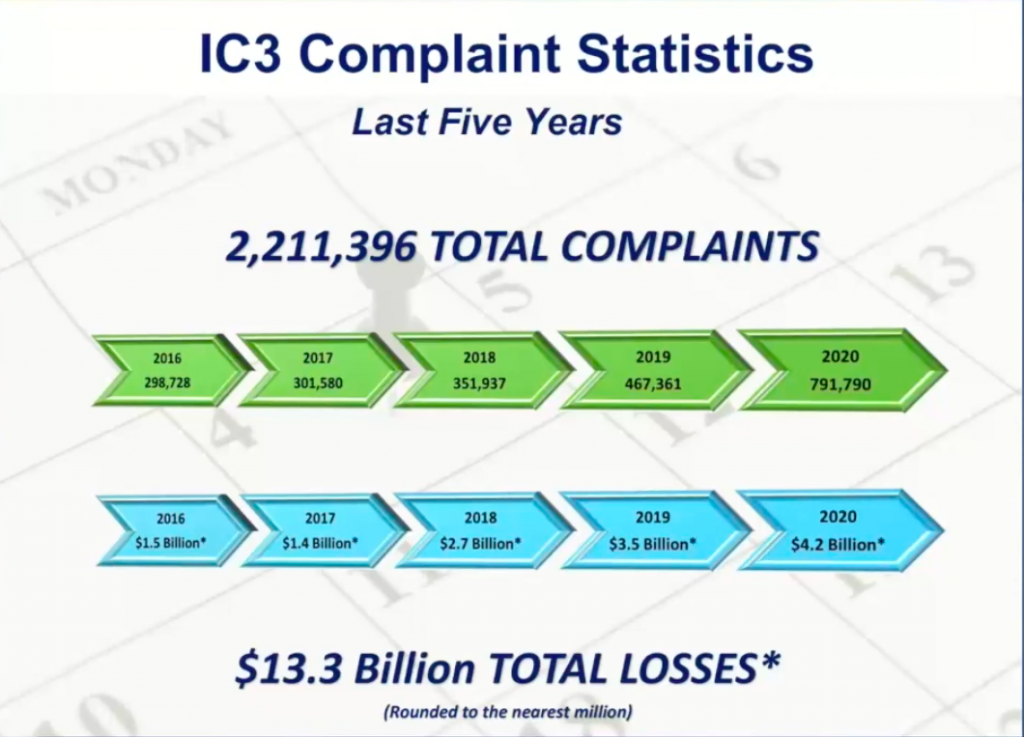
The graphic that you see is from the FBI, it’s their internet complaints center. So, they’re the investigative branch that is responsible for following up on cybercrime. And so, you know, as we’ve had kind of yet another recent example of cybercrime with the pipeline shut down as a result of ransomware, we really can see the financial impact that these attacks can have and how much it’s increased over time. So back in 2016, we can see that there were about a billion and a half dollars in damages reported to the FBI, and that’s real. I mean, that’s real money.
Just last year in 2020, that number is all the way up to over 4 billion and the number keeps continuing to grow. So we can really see that these attacks from cyber criminals, and I think that term is apt, there is a criminal activity engaged in stealing data that they kind of pivot and then turn often into a kind of financial extortion. So the number, the frequency and the sophistication of these attacks is increasing over time. And it’s not something that we see relenting anytime soon.
If we look at, I think the next slide here, in terms of how nonprofits specifically are equipped to handle this, I think this is an area where many organizations still have a long way to go. So, this is from a survey that NTEN did with Microsoft,
60% of organizations didn’t have processes in place to figure out how they would identify and manage risk, 74% of organizations hadn’t implemented, multi-factor authentication, 46% saying they’re using insecure Bluetooth and 92% of organizations are saying, “Hey, our staff can access our organizational data systems from personal devices.”
So, I think while nonprofit organizations in general have done a really great job of adapting and moving systems to the cloud and really having a flexible work environment, I think they’ve done a less good job in keeping up with the security policies and procedures in order to really protect that data. And I think it shows how much work still has to be done. And as an organization that supports about 140 different organizations, so we support about 5,000 nonprofit staff amongst all the different clients we see. A couple of years ago, we started to be really attentive to categorizing and reporting on the types of security incidents that nonprofits faced.
There’s lots and lots of data and lots of reporting from big commercial vendors that are talking about enterprise systems, and that’s great, and that helps inform our controls, but we also wanted to know what was specifically targeting nonprofit organizations. And so, we can make sure that we had the appropriate set of controls in place, because we know that with this request of prioritization, the answer is we can’t do it all. And so, we needed to focus on the most meaningful controls. So, we started our nonprofit incident report three years ago. So now with three years of data, we can really see some trends and some prioritizations. So this comes from our incident report which you can download from our website, but we can really see the amount and kind of sheer volume of email based attacks, both spam and spear phishing, or business email compromise along with a pretty significant increase in account compromises. That’s due largely to organizations not implementing that multi-factor authentication. So again, we see it, our service desk sees it in terms of responding to a lot of these incidents, and that helps to inform our approach to the controls that we recommend.
What is your risk profile
Johan: So, that leads us into a question of your risk profile. So, sometimes when you see these numbers, billions of dollars, and hundreds, you know, tens, hundreds of thousands of incidents, and you hear about a lot of the high-profile hacking that’s happening with large companies, like the pipeline. I think a lot of nonprofit organizations—it almost lulls you into a false sense of security thinking, well, we’re not running an oil pipeline. We don’t have billions of dollars. We’re not at risk of that kind of threat. And while that may be true, I think it’s important for nonprofit organizations to consider who their adversaries might be. And I think we all have adversaries, whether we want to accept it or not and it’s important to understand who those adversaries are.
So, for some, the most general adversary is the cybercriminal, and there’s a lot of money to be made in what might even be called petty cybercrime, you know, the wire fraud schemes that have been pretty common over the last few years, phishing attempts to get credentials.
Those are things that they’re not generating billion dollar payouts for the cyber criminals, but they can be lucrative. There’s a reason that those confidence schemes are still happening because they are paying off eventually. So I think at the very least, all organizations have a petty cybercrime as an adversary.
And then, organizations may have other adversaries depending on the type of work that they’re doing. So, if it’s an organization that’s doing policy—international policy work or national security work, almost certainly that organization is being targeted by nation state actors. If it’s an organization that’s involved in controversial social justice issues, it’s possible that that organization has adversaries that are opposed to their position on the issue that will be trying to attack them in various ways. So, that’s a good place to start.
If you’re thinking about the cybersecurity landscape, threat landscape, if you will, for your specific organization, I would start by thinking about who your adversaries might be. Who might be opposed to the work that you’re doing or what sort of everyday criminals might be interested in taking advantage of your organization and potential gaps in your security posture?
So start by understanding who your adversary is, and then assume the worst. Don’t assume that you’re gonna that you’re a small network. The fact of the matter is the nature of the tools that cyber criminals and adversaries are using, allows them to target millions of people at once, and so you’re not going to be able to hide through anonymity or through small size, if you have a presence on the internet, if you have email chances are you’re going to be targeted. So, start by assuming that your adversaries are coming after you, and they’re going to attack your organization, and then work to understand what the impact of those attacks would be.
If you fell prey to a fraud scam and someone in your accounting department wired money to a cybercriminal, what would be the impact of that on your organization? If your data was breached, or if you’re storing your data maybe with a third-party solution and it gets breached, what’s going to be the impact of that? Is your organization subject to compliance requirements? Are you subject to HIPAA? Are you subject to PCI? What would be the impact of suffering one of those cybersecurity incidents? So just kind of mapping out the risk profile, it sounds like a big fancy thing, and it can be—it can be very sophisticated, and you can go into great detail mapping it out, but you can also make a lot of progress in just answering these questions to your specific organization. And that can be a good start to thinking about how to address those cybersecurity incidents—and that can lead you into a consideration of standards and standards that you want to adopt.
Considering your organization’s standards
Matt: Yeah. So as Johan mentioned, there’s a certain set of basic minimum standards that every organization should have in place. This was the topic of last month’s webinar. So, I won’t kind of go down and detail this individually, but I do think it’s important that from my position as the CTO and kind of the technical respondent for a lot of these incidents is that, if these basic controls are in place, you greatly reduce your risk to falling victim to a variety of cyberattacks. I think every organization should take this list and make sure that they can check off the box to say with confidence that they have these things in place.
And it really starts with policy. I know policy is often hard to do because it’s a soft skill. It requires getting people together and agreeing on something, which is a little bit different than turning on a backup. You often just have to turn it on, doesn’t impact anybody, but starting with policy is a really great way to make sure that the decisions that your organization is making are aligned with the requirements that you may have in your organizational culture, to make sure that it just fits. So, starting off with policy is absolutely critical, and I would say that’s an IT acceptable use policy, maybe it’s a data privacy policy, and maybe you also need an incident response policy. There’s a lot of things that could go into that but start small.
And then basics, one of the things that we do for all of our clients is make sure that
- software’s up to date. May sound simple, but that’s a key element of making sure that systems are up to date and protected from known threats,
- making sure antivirus is installed, and then the big one I mentioned earlier is
- multi-factor authentication. I think every organization needs to make sure that that’s in place. Of the account compromises that we observed for our own clients last year, 97% of them did not have multi-factor authentication enabled. So, we can really see clearly from our data that if you have multi-factor authentication, you’re much more protected than if you don’t.
- And then kind of wrapping up, as I said backup.
Some of these controls are easy to implement in the background. They’re technology solutions. They’re very transparent to end users but having them in place means that you can recover if you have a ransomware attack or you can—in the case of spam filtering, you can prevent that malicious email from even getting into your user’s inbox.
- So then finally, what we really found is that having an equipped and trained staff is one of your greatest resources. So, there’s lots of great technology tools. We can put all kinds of fancy sophisticated software on your computers, but if people are not in the habit of clicking on everything that comes to their inbox, then that’s the best control that you can have.
So, I think there’s a certain set of minimum standards that I would expect every organization to have, and I think part of our conversations, how do you prioritize the things that have a much bigger impact that require more decision-makers or require prioritization because they are expensive or have other impact on business systems? I’d be curious, in the chat, if you have other controls that you’ve implemented, or you’d have some feedback in terms of this list. I mean, what are we missing from the list of foundational controls as well?
Johan: And of course, getting these things implemented is often the larger challenge. Do you want to say a little bit more about that Peter—with regards to some of the challenges? We left the challenging topic for you. We know what to do, we just don’t know how to get it done. But if you could give us some tips on that, that would be great.
Leadership’s view on the organization landscape
Peter: Well, because you mentioned change, I will just say, it’s not necessarily relevant to what’s on screen here, but we at Build—we say that every technology change effort is also an organizational change effort. There was this Jack Handey quote—”I went to a fight last night, and a hockey game broke out”—a number of years ago and it’s similar to that, that you can’t have a technology change project that’s not also an organizational change project. So change management is a big part of getting people to change their behavior. And that’s often needed for implementing many of these different security measures.
I did want to talk a little bit today about the executive director’s view of their organizational landscape when it comes to thinking about organizational strategic initiatives, relative to security initiatives. I mean, the executive director or any other senior level executive is looking at the broad landscape of things that are competing for their attention and competing for the organization’s time and resources. So for example, over the course of the last year executive directors and other leaders have been really focused on the shifting physical landscape of their work environments, sometimes closing down physical offices, definitely in most cases moving people to remote work.
Also, many have started up diversity, equity, and inclusion initiatives inside of their organizations. There’s been a real strong focus on revenue generation. Some organizations have felt the pinch of the economic woes and there’s just a host of other strategic initiatives that are both operational, such as those that I’ve mentioned and then are very mission oriented. And so, when you’re thinking about competing for time and dollars, what you’re most often going to want to do as an organization, and your inclination should be towards prioritizing the funds towards the execution of programs that serve your mission. Also, it’s easier to get funders to fund those programs than it is for them to fund the core or general operations, a lot of the time. So, when you’re a senior level decision maker inside of an organization and you’re thinking about security, you’re thinking about time and money invested in security versus revenue generation, and time and money invested in security versus investing that in program direct costs.
So, there’s a lot of competing objectives. Sometimes we call them competing initiatives inside of an organization. And so, if you’re an executive director and you’re thinking about something like adding an additional layer of phishing attack protection to email, on top of the spam filtering that you already have, and you’re thinking about the per user cost of that and any change that might be necessary to get that implemented across the staff. Then you’re also thinking about that in terms of time and attention relative to these many other initiatives.
A lot of the time at clients, I get asked the question “Well, how should we be balancing this next security priority relative to all of these other things that we have going on?”
And so, I often try to reframe set cybersecurity practices in terms of benefits that come along with their implementation. So that there’s a more tangible business benefit to the organization. So for example, if you’re at risk from having outdated machines in your organization or you have a lot of different machines and devices that you need to manage, that’s increasing the complexity of your security management landscape. There could also be great business benefits to be achieved by updating those systems from a productivity and mission effectiveness standpoint. Obviously, it serves a cybersecurity benefit, but it also serves a practical benefit and this is particularly true in organizations that have underperforming systems doing things like media asset or video processing, or data management for large scale data sets and things like that. There can be really a lot of problems and workarounds that need to be created from not having the right hardware resources in place.
And then for example, if you’re using an on-premises CRM system that has some known security vulnerabilities in it that have become too great to ignore, implementing a new cloud-based CRM system with multi-factor authentication, with a better sort of security perimeter baked into it and other security practices can be a big benefit to the organization in terms of managing constituent relationships.
So in many cases, there is a business opportunity that can be paired with cybersecurity risk mitigation or a cybersecurity initiative. And that does help to position those initiatives better and more compellingly against other potential strategic initiatives, whether they be program related or operational in nature.
Matt: I’d just jump in and say the shift to the cloud—I think in addition to being an access improver for many, many organizations, has really improved the level of cybersecurity controls because the things that you’re able to get with Google Workspace or Office 365, in terms of logging and reporting and analytics, far exceeds anything that you could possibly do with your on-premises environment.
By this time, most organizations have made that transition, but we still find— shockingly enough—there’s still the on-premises exchange server that’s lying around. There’s still a lot of on-premises legacy databases and file servers. When it comes to answering the question of, who accessed this file at what time and what did they do to it? If you have an on-premises file server, you just can’t answer those questions unless you’ve already invested in tools. Whereas if you’re on Office 365 or Google Workspace, those questions are really easy to answer. We can see, “Oh, this person accessed this file a week ago, nobody else accessed it,” and so you have a lot more insight because of that. So, I think that’s a really helpful insight, Peter, to kind of frame those other business benefits beyond just the security perspective, but I think the functionality and performance improvements as well.
Peter: We’ve talked a lot here about moving from the ancient to the modern from a technology standpoint, but there are also security risks that come along with the proliferation of self-service modern systems, and that’s no more the case perhaps than in the arena of file management. We’ll often work with clients who say, “Well, yes, all of our files are in secure systems in the cloud,” and maybe that’s primarily Office 365 or Google Drive, but then you come to find out after you do a survey that they also have files in Dropbox and Box, and as many as six or seven different file management systems and then also in Slack and also in all of these other places. And sometimes organizations really don’t know or aren’t aware of where their files are and that creates a security risk in itself. So more so than seeing clients move from an older system to a newer system, now I’m seeing them trying to consolidate and tighten their governance around the modern systems that they have, because there’s such a proliferation of them and that makes the security management landscape very difficult.
Matt: I think it makes it more difficult because we’ve moved from, you know, the IT department controls everything to now, everybody can sign up and adopt new systems and it’s really easy to do, and it doesn’t cost anything and it flies under the radar. And so, I think IT has a real challenge in making that transition from being the gatekeeper and they really hold everything closely, to being a bit more open and understanding the business needs of various departments. To say, all right, we’re in Office 365, but we understand you also need to collaborate with folks that are in Google. How can we make sure that we’ve got good security controls around our corporate Google workspace account, as opposed to everybody using their personal Gmail accounts? They don’t have the same data controls.
Peter: Yeah, that’s pretty common and I’ve had many clients that work with funders and clients of their own, that for a particular project are required to use a separate file management system. Maybe one that’s provided by the client or funder, maybe one that they just have all pre-reviewed and approved from a security compliance standpoint. There’s always going to be reasons for things to be in different locations. I think the key is being able to have knowledge of and create a policy umbrella that encompasses those situations.
Johan: Going back to your original point, Peter, about change management, oftentimes change management is addressing the culture of the organization and you can have great systems in place and you can have great policies written about how those systems are being used, but if the staff in the organization don’t have a security-first mindset, there’s nothing that really forces them generally to use those secure systems in a secure way, if they end up using Dropbox because it’s easier for them or for what they’re used to.
It speaks to the value of creating a security culture within the organization. And really, I think most staff that work at nonprofits are invested in the mission, they want to see the organization succeed. They’re not trying to put the organization at risk and if you can do a lot with staff education and really create a culture that prioritizes security and that will discourage staff from adopting their own solutions that may not be as secure.
Peter: Yeah, this is one of the points in conversations like this, where somebody will chat in, “Well doesn’t culture start with leadership?” and they say, yes, obviously. It all comes back to leadership in one form or another, right? And I know when we were talking about this topic in preparation, we were thinking about, well, what level of technology or security awareness does there need to be in those leadership roles in order to have an effective security minded culture? And what would you say the answer to that is Matt?
Matt: I think it takes all kinds. You don’t need to have somebody that’s an expert in security. I think what we’ve found the most helpful is somebody that’s really engaged, can ask good questions, knows the organization, is able to prioritize. So, I think some of our best relationships with our primary contacts are not technical at all and admit, or even boast about how much they don’t know about technology. But they’re really good because they know the organization. They’re able to take and receive guidance and counsel and then make those things a priority based on their input from outside experts.
Peter: Yeah.
Johan: That’s a great segue, Matt.
Incident response readiness
Peter: We talked about this earlier, but if you’re working to prioritize cybersecurity as an organization from leadership into a very cultural base for your organization, you have to start with that top level view of risk opportunity and investment.
So, we can get a good sense of what your risk profile is as we discussed before, but also what opportunities could come along for mitigating risk and how that helps move your business forward. How technology can serve as a catalyst or an accelerator for overall business improvements in your organization that can benefit programmatic outcomes and make investments accordingly.
And then we often encourage clients to say, “Let’s get together in a room today virtually and have a scenario-based exercise to clarify what kinds of things might happen.” Let’s walk through a security incident and see what we can do from a proactive risk mitigation standpoint to help avoid that in the first place. And then, what would we do if an incident does occur? And I think it’s worth mentioning that I believe roughly about 80% of the clients that I’ve served over the past 15 years or so have had a cybersecurity incident sometime prior to us coming in to help them as an organization whether it be an attack on their website or an attack on a network file server, or a compromised executive email account or a wire transfer fraud scheme—many of the things. And so, as Johan said it’s not so much a matter of if, but when. So, it really helps to just think through a couple of these scenarios and demystify what the risk is and then try to come up with a clear idea of what your incident response readiness level should be.
We’ve been talking a lot with our clients and I’m sure you guys at Community IT have as well about cybersecurity insurance over the past several years, that’s a component of response readiness in a sense.
Also, you need to think about, if constituent data is compromised in some way, what kind of communication should you provide to those constituents and when? Do you have legal counsel that’s prepared to advise you, or do you know who you could reach out to if you needed to speak to a legal advisor about how you should handle that incident? And so on and so forth, and we could talk at length in a future webinar about incident response strategy.
And then as we’ve been saying, it’s important to work to develop good habits with an emphasis on the mission, not on fear. We try not to sell cybersecurity measures through fear-based tactics. Unfortunately, there’s no way to get around that sometimes and it can be an effective motivator, but ultimately, we want to steer people towards and keep their eyes on, an opportunity to benefit or preserve the mission of the organization more than just, you guys need to cover your you-know-what in case something happens.
Matt: Yeah, I agree. I think the challenge is always getting attention and making it a priority, because I know that we’ve worked with organizations where multi-factor authentication has kind of been on the list for a while and we’ll get to it, and we’ll get to it, and then we’ll get to it. And then somebody whose account gets compromised and then all of a sudden they’re able to prioritize it and it becomes a doable thing for the organization.
I don’t like to be in that position of using those painful incidents as a way to kind of move cybersecurity initiatives forward, but sometimes that’s what happens. And so I think as much as the message can be communicated, like, hey, these things are really important and how can we make sure that we are prioritizing those things in the broader context, so that we can be proactive about cybersecurity and prevent incidents from happening as opposed to implementing controls reactively, after they’ve already occurred. And so, yeah, I think it’s a challenge, but I think as the advocate for the controls in the first place, I know that using those painful opportunities to move the organization forward is often what ends up happening.
Peter: And there are some arguments or incentives that fit between the opportunity and the fear-based approach. So for example, when I’ve had some clients in the past that are lagging behind in their security measures implementation, and maybe they have an executive director or some other senior executive that’s approaching retirement, I can start talking to them about legacy and what kind of an organization they want to leave behind them to support the mission through the next generation of workers and the next group of people that are going to lead the organization forward into the future. And sometimes in that way, you can get those kinds of initiatives wrapped into the things that that individual wants to accomplish before handing over the reins to somebody else. So, there are a lot of different ways.
And ultimately because of that, there’s a lot to be said for having good relationships with the people that you’re trying to develop these conversations with. It’s very much like data quality in that sense. It’s hard to come cold from the outside and just make the first thing that you put in front of somebody, how bad their current practices are and what they need to do to improve them. So yeah, relationships can sometimes be important. Particularly when an organization has recently been the victim of an attack or knows that they’ve been a victim of an attack and is just fresh coming off of that, and they’re saying we need to do X, Y, and Z to make sure this doesn’t happen again. It’s sometimes the hardest sell before the attack happens, not after the attack happens.
Johan: Yeah, I agree. I’m not a fan at all of the fear-based approach. I think fears and emotions are something that is a fight or flight response. Evolutionarily, fear is something that gets us to react very quickly in moments of immediate danger, but we can’t live in a state of fear over a long period of time. And so, it’s not a good emotion to try to leverage for: fighting for creating momentum around an IT roadmap, because the fear is going to go away. And if that’s your only motivation, you’re not going to have long-term sustained progress with regards to your cybersecurity posture. So, going back to a more rational approach where you’re identifying the risk in a sort of logical, credible way, I’ve found to be more effective.
One example: I was working with an organization that is in Office 365, and I was able to pull sign in attempts. Office 365 has made a lot of progress in its security center, and you can actually get a lot of very useful and interesting reports. I was able to show that one of the longtime staff who at one point had administrative rights within the organization, that his account was attempted to be logged in from 12 different countries across five different continents. That was a real wake up call. Just to say, in the last 30 days, there’ve been dozens of attempts to try to gain access to this account from this wide range of locations.
Peter: This person was not a traveler.
Johan: And yeah, this person was not going to all of these different locations and forgetting his password and trying to log in. That put it on the roadmap. But then you have to understand that most nonprofit leaders, senior leaders especially, have a lot of priorities. They have a lot on their plate and it’s up to whoever’s responsible for IT in the organization to keep coming back to, hey, we agreed to do this. This is important, right? We’re all in agreement on that. What can we do this week to get us one step closer to making it happen? You can’t expect the senior leadership to be driving it forward, but once you get the buy-in they’ll be open to you driving that initiative forward.
Peter: Yeah. I often when we come into clients, no matter what the technology need is, one of the questions that I often ask is, do you want to take this technology improvement project on to move away from pain that’s behind you or towards a reward that’s in front of you? Because I think understanding that motivation there is important. And I often think that moving from pain that’s behind you is—we were saying that fear, only gets you so far. It usually gets you to the point of mediocrity and not a lot farther than that. So at some point, the opportunity has to be the thing that pulls you forward, because otherwise, you’re just going to do just enough to get out of the immediate pain and then your attention is going to start to wander elsewhere. And that’s true if you say, well, our board questioned our constituent data statistics and asked how really good our data was. So, all of a sudden, we have to do a lot of deduplications of our Raiser’s Edge database. It’s true for recent security incidents, any kind of disruptive event that could cause the pain. Great, now we’ve got their attention. But what’s going to help to sustain that into the future?
Johan: We can do better than mediocrity. That should be our goal.
Peter: Jim Collins, who wrote the book, “Good to Great,” also wrote a companion piece called Good to Great and the Social Sectors. And he said at the time, there was a major push to improve the nonprofit sector by bringing practices from the for-profit community into nonprofits. And he said, don’t do that because most of the practices in the for-profit sector are mediocre and we have enough mediocrity in the social sectors already. So, we definitely want to take best practices and move them over inside organizations and have it be very opportunity oriented.
At what point are security measures good enough?
Johan: So, I have a couple of questions that I wanted to ask the panel today. The first one has to do with diligence, that maybe speaks a little bit to mediocrity. We don’t want to stop at a point of mediocrity, but we also have to recognize that there are a lot of other priorities. And at what point are security measures good enough? At what point have you reached—you can always add more security. You can always encrypt it again. You could have three factor authentication. There’s more that you can do. At what point is it good enough? And when are you—when do you reach the point, do you think? When is it okay to start prioritizing other business priorities ahead of security layers, whether in terms of financial investment, time, messaging to staff?
Matt: Yeah. I mean, there’s foundational controls that I think absolutely must be in place, and I would say that it’s important to start there. I think I would also advocate for—I think security is an iterative process and I think there’s always new and evolving threats and risks out there and so, it’s never static. I think some of those changes are going to be, in terms of how much is good enough is going to be driven by some external parameters, as well. I know that we’re doing a lot of cyber liability insurance application support for our clients and the number of checkboxes on those applications this year as compared to three years ago, it’s really, I mean, it’s really notable in terms of how much more stuff they’re asking for as part of those controls.
And so, I think you’re going to have to just keep moving along. I think for the organizations that have been able to make that shift, and I liked your analogy, Peter, in terms of moving away from pain to moving towards an incentive or an opportunity. The organizations that have been able to make that shift, they’ve maybe gotten some good acceptable use policies in place. They’ve turned on multi-factor authentication, they’re kind of doing the foundational stuff. I think it’s easier for them to keep going and maybe they need to add another security control or perhaps, whenever they’re evaluating their vendors, they’re able to incorporate some additional questions in terms of how the vendors themselves are handling their data and what processes and protections are in place there?
And so I don’t think it’s static. I do think you probably have to get over a hump where you’ve changed the organization’s mindset a little bit. I think it has changed a lot in the sector, especially I don’t think we run into too many nonprofit organizations where technology is viewed as a necessary evil. Again, I think they still exist, but in general I think many, many—most people see technology as an enabler and it allows them to accomplish their mission and do all this great stuff.
And I think on the cybersecurity side, it’s probably similar to that too, you need to get over the hump. Make sure you’ve got your baseline controls in place. And then build it into the practice of the organization to have that security mindset, regardless of the initiative that you’re implementing. I think there’s going to be a vein of how you’re protecting and managing and storing and accessing that data no matter what system or process you’re getting ready to implement.
Peter: Yeah, I agree. It’s different for every organization based on your risk profile. And that risk profile can include the tech savviness of your staff at times. Sometimes less tech savvy staff can create a greater risk profile. An example that I sometimes come back to is, let’s say you already have some sort of threat protection perimeter on your email like, something that’s baked into or available through Office 365, and you know that’s going to catch a certain large percentage of the threats that are coming through, and then you invest in a little occasional cybersecurity awareness training for your staff. At that point, there might be a good argument to invest in a non-security related initiative rather than taking the next step, which might be saying, adding an additional phishing protection layer like through Barracuda Sentinel or something like that.
But again, it’s a judgment call and I would recommend going ahead and doing the Sentinel for the amount that it costs on a per user basis. But if an organization is saying, look, we really need to invest some additional money in digital engagement or else there’s not going to be any money to spend on Barracuda Sentinel. So, at that point you have to say, okay, I understand that we’ve laid out a basic layer of protection. We’ve done this training; let’s put that Barracuda Sentinel idea on hold for now and maybe come back to it in six or 12 months after we’ve had an opportunity to bolster up this other area. That’s of great strategic importance. So, that conversation is going to run a little differently for each organization, but that’s an example that I see fairly regularly and actually one that we had to think about inside our own consulting firm. How much protection is enough protection for a tech firm with good technology savvy and awareness? So, the same kinds of concerns that nonprofits are juggling. They’re not unique to the nonprofit sector. They affect us as well.
Tips for securing buy-in for security improvements
Johan: So, let’s talk a little bit about buy-in. I’ve talked about this a little bit earlier, but
- What are some tips you have for ways to make the case for security improvements at executive level?
- What are some things that you’ve found to be effective in making that case?
Peter: First of all, you have to make sure that you are having a conversation at the executive level, because if you’re not already having that dialogue in some way, it’s hard to jump into it with security risk as your lead conversation point.
But for us, we’re often talking with clients about broader technology issues and are including security as an aspect, if possible. In this technology related initiatives are to be prioritized within a broader roadmap, and sometimes even something like an ERP or CRM replacement project is an opportunity to introduce new ideas about security, whether it be third-party data access or multi-factor authentication or single sign on to make MFA a little bit lower friction for employees or a variety of different things.
But again, ultimately it relies on being able to have access, to have the conversation at that executive level, and then try to make a business case for the security improvement that introduces both risk and reward as possible, and also acknowledges that there are many other important initiatives inside of the organization that are going to vie for attention with this particular security improvement.
One of the biggest challenges that I’ve seen in the past with IT clients getting traction on security issues is partly that no prophet is without honor, except in his own country, right? So, if you’ve been the one that’s beating the drum for a long period of time, sometimes it’s good to have a fresh voice. And I’m sure you guys see that as well with clients that you’ve been embedded with for a long period of time, but it also is the case that sometimes internal IT will take a hard line and say, well, this needs to be the organization’s number one priority right now. And maybe sometimes, or even oftentimes that will be true but if it comes from an uncompromising lack of awareness of the other challenges and opportunities that the organization is facing, it can really fall on deaf ears This is more to say that whoever is working in the technology space inside of a nonprofit, or as an outside consultant into a nonprofit needs to be able to think with the mind of the organization, when they’re thinking about security related initiatives.
What are your thoughts, Matt?
Matt: Whenever we’re being brought in, I think one of the helpful drivers does tend to be those external compliance sources. So again, formal compliance standards like HIPAA or PCI can help drive that conversation because it’s a mandate. They have to pay attention to that. I think as I mentioned cyber liability insurance, again, we’re seeing many, many more organizations take that up, and so there’s additional controls listed there. I think we’re also seeing the encroachment of finance audits into the realm of cybersecurity, and so now all of a sudden the finance audit includes 10 questions about the cyber controls at an organization. And so that’s been an avenue in terms of getting executive attention, executive buy-in in terms of having these initiatives come forward.
I would say that in general we’ve seen initiatives be successful both from the bottom up—whatever in-house tech people say, hey, we really need to do something about this and move it up the chain. And then we’ve also seen initiatives be successful as kind of board mandates down into the organization. The board says we need a cybersecurity assessment, and we need to really improve this as a strategic initiative, and I think the common thread there is both the executive layer level being engaged and making it a priority because it’s almost impossible to do without that. As the tech implementer, there’s a couple of things that we can do kind of behind the scenes to make an organization more secure, I think to really implement that full level of controls it has to be a change management process.
People have to know and acknowledge and participate in those changes and tech can only do so much on its own. And so, we often do end up implementing a lot of the technology controls first, because it’s easy to pay $3 a month and turn on a widget that makes things better than it is to schedule a training for multi-factor authentication or to schedule a security awareness training, but again, in all those cases, the executive needs to identify this as an initiative that’s important for the organization and give it credence.
Peter: I do think it’s good to also come into the exec with that quick win though, because sometimes the thing that can be done the most quickly with the least amount of pain, even if it may not contribute the biggest result, can be a catalyst for moving towards things that require a little bit more involvement. So that’s an opportunity as well when you’re talking at the executive level. You can say, hey, just for this small per month transaction fee, we can have this layer of security. We can all celebrate it and it won’t require you to do anything. So, that speaks to our human nature and also to the fact that not every security enhancement needs to be a huge lift.
Johan: Yeah. Go after that low hanging fruit. We are running up against our time here. I think we’ve discussed this last question that I had, how we can help nonprofit leaders to understand the value of making and enforcing security policies. I don’t know if there’s any final thoughts you want to—either of you would like to add to this?
Available resources and next steps
Peter: There’s a lot of resources in the Community IT website and the resources section that speak to this, I believe, and also there are some resources on the Build Consulting website, buildconsulting.com, in the blog about how leadership can engage in tech projects, and that would address both the previous slide and this one. So, there’s a lot of quick and easy resources there for you to access and I highly encourage you to reference them. And some people have even been known to forward such articles to decision makers inside of their organization to let somebody else beat the drum for them and make the case when it’s been a little bit difficult for them to do so from their position.
Johan: Great. So quick wrap up, Matt, you want to send us on our way with a few action items we can take moving forward?
Matt: Sure. I always think it’s good to have some specific takeaways from these kinds of sessions. So I think things that I would advocate for would be
- review your existing controls. It’s always good to know what is already in place before you start to think about reinventing the wheel.
- I think understanding your risk profile is really important. An organization that provides, as a social service organization, that has lots and lots of staff working on shifts is going to have a very different risk profile than maybe an international policy think tank that works on international trade issues. And so I think that would lead organizations down very different paths. So, I think there’s not a one size fits all solution, and these solutions could be uniquely tailored to your organization.
And then finally, this may be—I think this is something maybe is not just for the small organizations, but all up and down the line—but
- incorporate that cybersecurity into the budget planning. Peter made the comment, I don’t necessarily think cybersecurity should be its own silo, kind of off to the side, but I think it should be incorporated as an element across many different programs and initiatives, but it does need to be considered explicitly.
- The bonus one would be to look at that control from early in the list, make sure you’ve got those basic cybersecurity controls in place at your own organization. Again, I’ll use it as an opportunity to say, multi-factor authentication is the number one thing we’re advocating for right now.
Johan: Great. Thank you. Before we let you go, we just wanted to announce next month’s webinar. This month we were a little bit late. We were the fourth Wednesday of the month. So, the next one’s going to be up before you know it. It’s going to be June 16, just a few weeks from now and we’re going to be talking about Microsoft Business Voice. Is there anything Microsoft can’t do? Won’t do? Won’t try to take on? Microsoft has some very interesting and potentially compelling Voice Over IP telephony solutions as part of their Microsoft 365 Suite, integrates into Teams. Very interesting stuff. Matt’s going to be back again next month. He’s going to be interviewed about his experiences with that.
So, if you have any interest at all in simplifying your telephony solutions, if you’re interested in finding out more about what Microsoft is doing with telephony, we encourage you to come back next month.
So I just want to close by thanking Matt and Peter for your time today. This was a really interesting discussion and I have a feeling we’ll be discussing cybersecurity again before too long, so you’re not off the hook yet. Anyways. Thank you both. Have a good afternoon.
