Here are some links to get you up to speed on the basics. Matt Eshleman, our CTO and resident Cybersecurity expert, has been implementing encryption and works in partnership with clients to ensure end users have a simple experience, and that our nonprofit clients understand what is being encrypted, how encryptions works, and why we do it. So, what is encryption for nonprofits?
Although it sounds like a very “techie” topic, many of Matt’s webinars on cybersecurity delve into the practical applications of encryption. If you know nothing about encryption outside of spy novels, or are an experienced nonprofit IT professional looking for some up to date tips, please join us – all our webinars are presented in a format appropriate for a varied audience, and are a friendly forum for all level of questions.
What is encryption?
This article from the Telegraph Technology Intelligence group (required free site registration to read) explains the concepts of secure communications particularly well:
“A decent analogy for encryption is the digital version of sending something in a locked safe. Only those with the right key can get in…
Encryption … means that communication is scrambled in some way. A message could still be encrypted and deciphered by the third party – a government or tech company – if they had a way to unlock it.
End-to-end encryption, on the other hand, means that a message is encoded in such a way that only the sender and receiver can see it.”
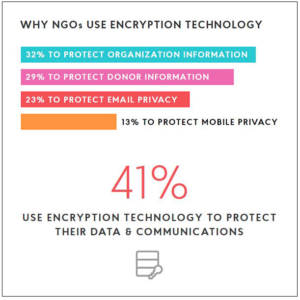
Why do NGOs (Nonprofits/Non Government Organizations) use encryption?
This blog post includes links to five other useful topics such as bitcoin and artificial intelligence, and links to further resources on encryption with nonprofit uses in mind.
What about a list of examples of products to encrypt personal data and communications?
This article from Wired on how to encrypt all the things gives a good run down of several apps and products, and includes links to further resources including extreme security measures for the extra paranoid. (Wired limits free articles to 4 per month)
“…anyone with a vested interest in keeping their communications away from prying eyes has no shortage of options.
In fact, secure communications are not only attainable but perhaps even the new default, says Matthew Mitchell, the founder of security training organization Crypto Party Harlem and an adviser to the Open Technology Fund. “Security is here to stay. It’s now expected that a product just encrypts without you having to do anything,” Mitchell says. He describes every unencrypted internet-connected app or web tool as a window without curtains. “Now people are learning there are curtains.”
…The best way to encrypt data at rest—rather than messages in motion—is en masse, by encrypting compartments of your storage, or simply encrypting your entire hard drive.”
Even if you are not ready to always put a blanket over your head and keyboard in a hotel room as Edward Snowden did (see the Wired article on extreme paranoia), please plan to join us for Encryption 101 for Nonprofits with Matt Eshleman, our CTO and resident encryption expert. As the costs of hacking personal information fall and our databases and communications are increasingly targeted, even nonprofits not involved with international intrigues can benefit from basic security measures.