Transcript below
View Video
Listen to Podcast
Like podcasts? Find our full archive here or anywhere you listen to podcasts: search Community IT Innovators Nonprofit Technology Topics on Apple, Spotify, Google, Stitcher, Pandora, and more. Or ask your smart speaker.
2021 Cybersecurity Readiness for Nonprofits Playbook
Join CTO Matthew Eshleman for the release of our newly updated 2021 Cybersecurity for Nonprofits Playbook.
Is your nonprofit prepared? Learn the Community IT approach to cybersecurity and how to implement the changes you need to protect your organization.
Matt shares advice on security improvements that provide protection against the most common attacks. You will also learn about staff training, cyber insurance, and why you need written IT documentation and governance policies.
This Playbook gives you a structure to understand cybersecurity risks. Matt’s presentation gives you tips you can put in place quickly and train your staff on immediately. You can download the new Playbook for free here.
This webinar is appropriate for nonprofit executives, managers, accounting, development, and nonprofit IT personnel – and as with all our webinars, it is appropriate for a varied audience.
Community IT is proudly vendor-agnostic and our webinars cover a range of topics and discussions. Webinars are never a sales pitch, always a way to share our knowledge with our community.
Presenter:

As the Chief Technology Officer at Community IT and our resident cybersecurity expert, Matthew Eshleman is responsible for shaping Community IT’s strategy around the technology platforms used by organizations to be secure and productive. With a deep background in network infrastructure, he fundamentally understands how technology works and interoperates both in the office and in the cloud.
Matt joined Community IT as an intern in the summer of 2000 and after finishing his dual degrees in Computer Science and Computer Information Systems at Eastern Mennonite University, he rejoined Community IT as a network administrator in January of 2001. Matt has steadily progressed up at Community IT and while working full time received his MBA from the Carey School of Business at Johns Hopkins University.
Matt is a frequent speaker at NTEN events and has presented at the Inside NGO conference, Non-Profit Risk Management Summit and Credit Builders Alliance Symposium. He is also the session designer and trainer for TechSoup’s Digital Security course. He presents updated tips to protect your login credentials throughout the year.
Matt is excited to present this completely updated 2021 Cybersecurity Readiness for Nonprofits Playbook.
Transcription
Johan Hammerstrom: Welcome to the April 2021 Community IT Innovators webinar. Thank you for joining us for today’s webinar Cybersecurity Readiness for Nonprofits. Today we are going to provide you with the latest information on how to protect your organization from the wide range of cybersecurity threats now faced by nonprofits.
I’m really looking forward to hearing more from our CTO Matthew Eshleman about this very important topic. My name is Johan Hammerstrom, I’m the CEO of Community IT, and the moderator for our webinar series. The slides and recording for today’s webinar will be available on our website and YouTube channel, later this week. If you’re watching on YouTube, please subscribe to our channel to receive automatic updates, when we post new webinar recordings.
Please use the chat feature to ask questions throughout the webinar, and we’ll do our best to respond. Before we begin, we would like to tell you a little bit more about our company. Community IT is a 100% employee-owned company. Our team of 37 staff is dedicated to helping nonprofit organizations advance their missions through the effective use of technology.
We’re technology experts, and we’ve been consistently named a top 501 Managed Services Provider by Channel Futures and we received that honor again in 2020. And now I’ll hand things over to our CTO Matthew Eshleman. How are you doing?
Matthew Eshleman: Hey I’m great, thanks Johan, for the introduction. Love to hear that intro, that 100% employee-owned company, it’s great to work with so many great employee owners at Community IT and of course we get to work with so many wonderful nonprofit organizations, and I’ve gotten to do that for quite a long time.
So I’m happy to be here today to talk about the Cybersecurity Playbook for Nonprofits and get to join you this month. It was last year in February we talked about the cybersecurity incident report, and I look forward to seeing how those results, from the incident report, have now made it into the playbook in terms of recommendations.
So let’s go ahead and get started. You should have all gotten a link to go ahead and download the Cybersecurity Readiness for Nonprofits Playbook from our website. I think you may have to jump through another form capture but go ahead and I encourage you to download that. It did go out earlier today. If you’ve already had a chance to read it and to take notes, that’s great. I would encourage you, as Johan said, to go ahead and just chat them in.
We do have some time for Q&A at the end, but also if there’s anything that strikes you during the webinar, during one of my slides, I would really invite that conversation. So Johan will be managing that back channel, and we’ll have some time for conversation at the end as well.
Agenda
So to talk a little bit about our agenda:
- start with a little bit of background about the cybersecurity landscape that we find ourselves in now. I think it’s good to level set the operating environment that we find ourselves in.
- We’ll talk really briefly about educational technology, this cybersecurity playbook is really focused on regular organizations and the challenges that they face. We think Ed Tech is a little bit unique in that regard, so talk briefly about that topic. Again if you have questions, please free to chat them in.
And then really spend the bulk of our time diving into the
- actual playbook itself and the recommendations that we’ve made there in the three different categories, which we’ve framed out as being
- foundational cybersecurity controls,
- those that we’ve deemed as proactive and
- those that we’ve talked about as being optimized.
And then finally, I think it’s really important that we spend some time talking about how we can take these recommendations and move them into action.
There are a ton of other cybersecurity playbooks out there; there are lots of other resources that are available. I’m really glad that you’ve chosen to spend some time here with me going over what we see as being appropriate for nonprofit organizations, but I think all the recommendations and the playbooks in the world don’t really make much good if we’re going to kind of read them and acknowledge them and maybe put a plan and put it on the shelf.
So I think it’s important that as part of the playbook, we have some time to map out, how we’re going to take action and implement some of the recommendations here.
So let’s go ahead and get started with some background information. So here we have the – some graphics that are from the FBI’s IC3 Complaint Statistics. So this is representative of the data from the last five years.
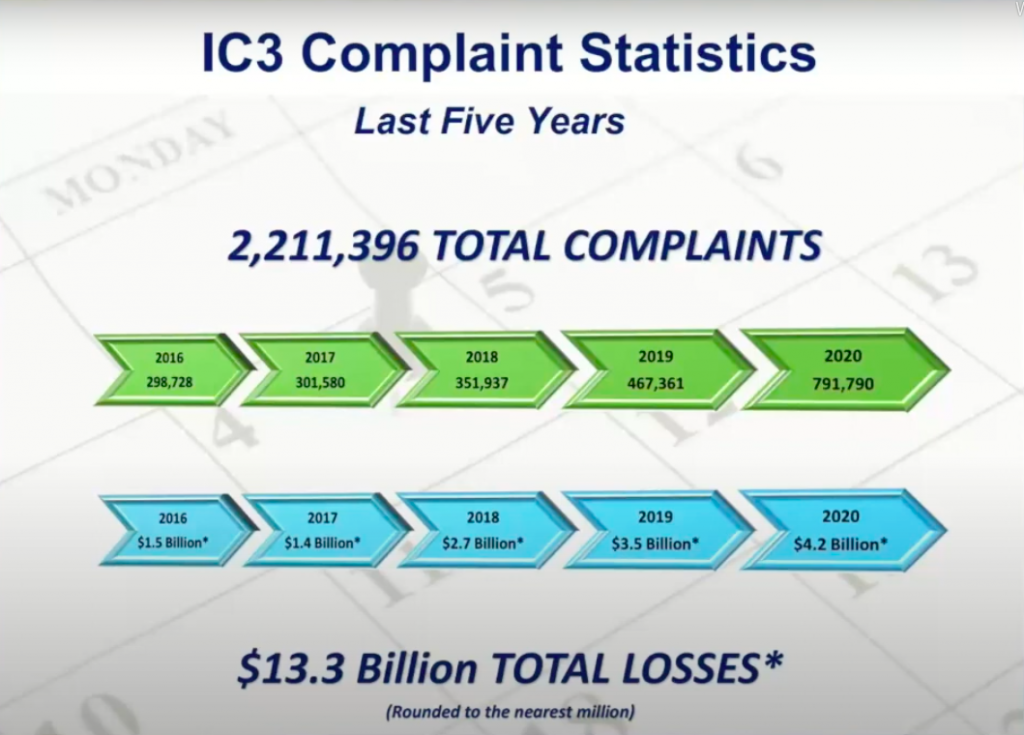
If you may have been involved in some sort of cyber crime activity, you may have reported that to the FBI. They compile all that data and then generate a report. And so we can see here pretty clearly that in the last five years, the number of complaints has steadily increased, and then along with the amount of financial damages that have been caused by cybersecurity incidents.
Over $13 billion dollars in total losses and that’s direct financial loss reported and investigated by the FBI. And so we can see that in 2020 that number is over four billion dollars. So clearly cybersecurity issues represent a real and significant financial impact to organizations and people, and it’s important that we as organizations are taking steps to secure the data that we have access to.
Before we get too far into that, I did want to get a sense of the folks that are here today, and one part of that is just getting some questions. So again a question here: I want to see how many folks attending the webinar today have gotten some IT policies at your organizations. You can just chat that out. So does your organization have a comprehensive set of IT policies? It could be yes, no, maybe just acceptable use in the employee handbook so go ahead and chat that out. We’ll leave that open for a second or two here as we get a sense for where the audience is today.
So great, thanks for chatting that out, I’ll reflect that back out. So we can see that most folks (54%) attending today are in that category where they do have some IT compliance policy language just in the IT handbook. With the smallest percentage (19%) saying yes, we’ve got a set of comprehensive policies. I think there will be something here for everybody for organizations that are just getting started and maybe need to work on some foundational security controls to those organizations that maybe have done some of the policy work already, and then are ready to move on to implementing some more sophisticated or complex controls to help improve the security of their organization.
And then since I got you here, I will do one more slide, which is how many organizations have implemented multi-factor authentication? So you’ll see some choices there, in terms of yes, you’ve implemented it for all staff, for some staff, just the admins, or not at all. Multi-factor authentication, we’ll talk about it later, combines something that you know which is your password, and then something that you have, which is often a physical, like an authenticator device. Most often that’s going to be an app on your phone, but it could also be a physical token for certain cases. So again, curious to see where folks are at in terms of the implementation of multi-factor authentication.
Okay. So thanks for providing that insight, I think it’s super helpful and it looks like, relatively evenly distributed between those organizations that have done it for all staff, which is great 35%. 31% for some staff, very small number of admins only and then about 30% of you have said no, not at all. So if you’re in that category, hopefully by the end of this presentation, you’ll be convinced that’s the number one thing that you need to tackle. So thanks for sharing that. I appreciate the information from folks here on the webinar today.
And also I wanted just include that so we could reflect how you’re doing compared to the overall internet sector at large. This was taken from a report that Microsoft put together, I think we have the link for that. Microsoft put out a report called Nonprofit Guidelines for Cybersecurity. Along with NTEN. It’s representative of a survey of about 50 organizations, so actually not that many, compared to the sector as a whole obviously. But in that sampling we see that most organizations (60%) didn’t have a policy in place, in terms of how they would handle risk. The vast majority (74%) of those organizations had not implemented multi-factor authentication.
So, congratulations, you are doing better than average. And also it may be reflective. This was about two years ago, so we can see there has been some progress over time. Most organizations didn’t have a policy around the use of unsecured wireless or Bluetooth and a large number of organizations (92%) reported that staff could access information through many devices.
So there are no BYOD policy controls, no technology controls in place either, to help protect organization data and put up some guardrails. I think it’s interesting to see these numbers, and I think interesting to see how they change over time. I would say at Community IT, we would have probably 65% of our clients have enrolled staff in multi-factor authentication for all users so I think we’re doing a little bit better than average, but I think that there is still a long way to go in that regard.
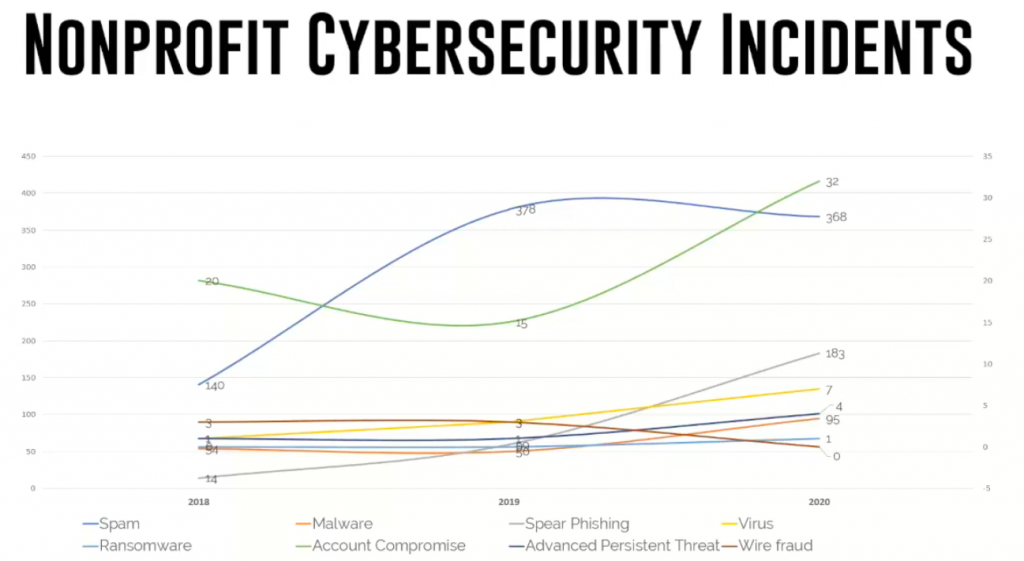
Specifically talking about the nonprofit cybersecurity incidents, this is the big chart that came from our presentation in February, where we looked at the nonprofit incident report, which is a collection of all the data that we’ve gathered in supporting about 5600 across the U.S., in terms of their cybersecurity incidents. The things to highlight here, I wanted to show that we’ve got a lot of account compromises.
There are two different scales here, so just be mindful of that, but the number of account compromises was up, even as we had more and more organizations involved in multi-factor authentication.
The number of spam incidents continues to be very high, indicating an increase in training and awareness and we encourage our clients to submit those messages, if there is ever any question.
And then we also see there’s a big increase in what we would call Business Email Compromise or spear phishing.Those are the types of messages that combine some unique information about you and your organization, so the threat actor can get you to do something, provide a username and password combination, maybe buy a gift card, maybe update a wire transfer information. These are all types of very common threats that we see facing nonprofit organizations.
And the number of incidents has only grown over time. We first compiled this report with data from 2018. And that year we recorded 233 different security incidents. In 2019, we recorded just over 500 security incidents and then last year we recorded almost 700 security incidents. We can see the number of incidences only increasing over time. I don’t think we’re going to get to a point where there’s less need for cybersecurity controls and so to some extent, there’s an ever pressing need to continue to grow and evolve and improve the protections and controls that we have in place at our organizations.
Cybersecurity for Ed Tech
Taking just a note to talk about cybersecurity for Ed Tech, I would say that some of the same principles apply. We typically think of Ed Tech in a couple of different categories: we have administrative staff; we have teachers; we have students. All the data needs to be protected.
There does tend to be some unique operating environments and or operating challenges in support, particularly student access to information, with COVID and so many organizations going virtual, throwing so much online, technology and students with so many different passwords to manage and access. Taking deliberate control to protect those accounts and that data is very important.
Additionally, we do see schools being targeted by ransomware actors. In Baltimore County, they’re still suffering from the effects of a massive ransomware campaign that impacted their school district back in November of 2020. For information on that, you can go to our website where we have a set of best practices that we’ve developed, focussed specifically on cybersecurity for education space and I encourage you to follow that.
I think the rest of the presentation today will be focused more on organizational cybersecurity controls. I think they’re all still relevant as well, just acknowledging the education space operates a little bit of a unique environment.
Our Approach to Cybersecurity
So, in terms of how we approach cybersecurity and approach these controls, you may have seen this graphic before. Recognizing that we want to root everything in security policy.

We want to build on that with a layer of security awareness training that we’re providing to staff. We’re equipping our users with the tools and education they need to help protect the organization.
And then finally we get to the technology control piece. So there the technology controls focusing on those elements around our digital identity. The data that we have access to, the devices that are being used to access that information, the network perimeter, such as it is. In this COVID and work from home environment, perimeter list maybe is a better analogy. Your home office, your home computer, that may be the extent of the network perimeter.
Then also, the access of websites, both the website of your organization and the web properties of your organization. And how you are getting to the internet yourself as a consumer of technology.
And then layered on top of that is this idea that there are new and, I think, pretty cool elements of technology that really incorporate some AI and some machine learning techniques to help improve the security to provide better technology solutions to help secure organizations.
Moving from how we look at security into our assessments, those eight different areas, representing those controls in a maturity model, we have broken them up into just these three categories of foundational, optimized and proactive.
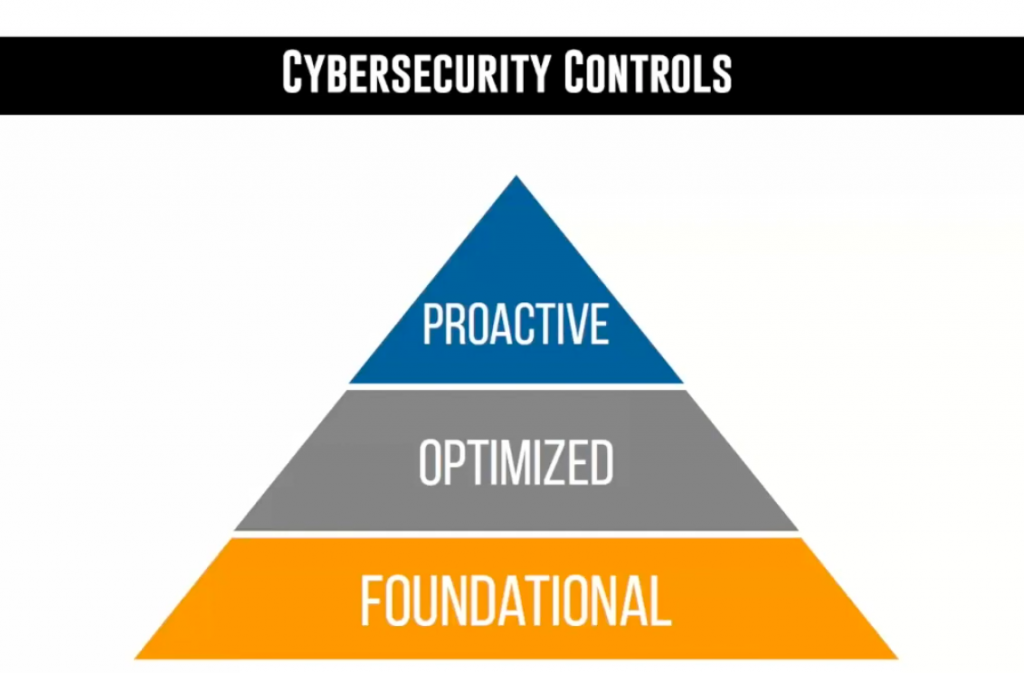
You could argue that there could be a lot of gradations there, but it’s important that we have a sense of, walk before you can run. Maybe that’s the analogy here. Spending a lot of money on high-end security tools, you may get some benefit out of that, but if you haven’t been able to implement the foundational controls, there’s still going to be significant gaps in what your organization is exposed to.
I find it helpful to look at these controls through these different lenses, again, it’s not an all or nothing approach. You may choose or be able to implement some things in the proactive level along with foundational or optimized. This is not Maslow’s Hierarchy of Needs where you have to have everything satisfied before you can go on to the next level, but understanding if you’re choosing to make some investments, I would definitely recommend starting with the foundational layer to make sure that you’ve got those key elements in place.
Also in the report, I did want to highlight that I included some budget numbers to help provide some context to the recommendations that they’re making. They are ballpark costs, I would say based on an organization size of about 25 users. The dollar cost that you will see in the report itself are good budgeting estimates that would include the cost both of the technology and if there’s technology solutions or people cost in terms of either external consulting from us or even cost from your own organization in terms of time, energy, focus to get some of these things implemented ranging from low cost solutions maybe free to $2000 a year, all the way up to solutions that may be more than $15,000 a year to implement.
In the cybersecurity world, there can be a whole range of costs whenever we look at the options available to us, so in the playbook itself, there are some budgetary guidelines that you can use to get a sense of how much a particular solution may cost to get implemented.
Foundational
So with that being said, let’s go ahead and jump into some of the key foundational controls.
You can see here that we do start with policy. Tying back to that first question I asked, how many people had IT Acceptable use policy? I think we were at about 50%, had some elements of that in their employee handbook, that’s great. I would say start there, it probably needs to get built out a little bit.
And then in addition to what would be a general IT Acceptable use policy, governing what you can and cannot do with an organization’s computer or IT systems. I think it’s also important to include elements of data privacy, as many nonprofits are either providing services to people and have potentially sensitive information collected about their constituents, they also may have donor information about the people that are supporting them financially so that data privacy policy is an important element as part of those foundational controls.
It’s also important to include a formal incident response policy as part of your foundational controls. We have a link on our website to guidelines for establishing what that incident response policy needs to contain and needs to include. Many non-profit organizations were shocked into creating one last year when Blackbaud suffered their data breach of their hosted platform. Many organizations really needed to scramble to come up with and execute an incident response plan because of the external factors that they were thrown into. So this is an area where the incident response policy doesn’t need to be very extensive, it doesn’t necessarily need to be very lengthy. But it does need to be articulated.
It does need to be tested, so that if and when, and maybe not even if, but a question of when your organization suffers some sort of data breach either of a hosted system, maybe your internal network. You have a clear roadmap to follow of who needs to communicate with stakeholders, what your technology provider is going to do. Make sure all those roles are clear, so that it can be executed whenever you’re in a stressful situation.
Then the final element here around policies, is an insurance review. You’ll see that we talk about insurance later on as well. But again, I think it’s important to understand what’s included in your current insurance policies, I would also highlight that I worked with TechSoup to develop a cyber liability insurance course that you’re able to access there. It’s low cost, just to get some understanding of what all is involved when it comes to cyber liability insurance. Understanding how it is different from your existing liability and property liability coverage that you have.
Moving into controls around security awareness at the foundational level. You may be able to take advantage of free or very low cost staff training, again through TechSoup. There’s a free 101 and 201 cybersecurity course that’s available as part of their partnership and grant with Microsoft that I developed.
This year, I also did cybersecurity training as part of our monthly webinar series that’s available free on YouTube. That’s great to get started providing some basic education to staff. As I said, you can invest a lot of money in expensive technology controls, but if your users are just going to click on links and open stuff and use technology poorly, they’re going to subvert all those technology controls. It’s important to focus on staff education and training. And enlist them as allies in your goal to protect the organization’s data.
Technology Controls
Moving into some of the foundational technology controls, this list seems to get longer and longer over time inthe number of things that are key and every organization needs to have in place.
It really does start with multi-factor authentication. We see that the threats and the attacks on online identities is the biggest risk that’s facing organizations. And so judging by all the logs that we look at, they are ongoing persistent brute force attacks against any system that you can log into online. Protecting that digital identity is absolutely critical for protecting an organization’s data. Turning on multi-factor authentication involves something you know, which is your password and something you have, which is an app on your phone in most cases. These controls are often free to implement; it takes a little bit of staff training.
“My sense after having done quite a few of these is that staff are really good and comfortable in signing up for these services with a little bit of training and help. “
It’s not that big of a time investment for an organization to make this transition. The technology is available and it’s really easy to adopt.
Following on the heels of protecting identity is focusing on the password manager. You’ve heard me talk in other sessions. My message is: you basically need two passwords. You need the password to your computer, you need the password to your password manager. Everything else should be automatically generated and stored within the password managers so that you’re choosing new complex, unique passwords for every different system that you’re logging into.
I have access to hundreds and hundreds of systems. I want them all to be very secure through passwords that I can’t remember. So every time I’m using a system, I’m generating a unique password and if that system ever gets compromised, then it’s not going to lead to an exploit of other systems that I have access to.
Password manager is a really key element of those foundational service security controls. There’s a number of them out there. I use LastPass. I know Dashlane is available on Techsoup for a bit of a discount. There’s 1Password, there’s a lot of different tools out there that can help make managing passwords a lot easier.
Backups are also on our list of foundational controls. I think it’s also important that we acknowledge that as data has gone to the cloud, many of us think it’s out of sight out of mind and the provider is going to back it up for us. That’s not necessarily true. Our recommendation is that for any data that you have in a cloud system, you also need to have that data backed up somewhere else that you have access to.
The providers are going to protect your data to some extent, but they’re doing it to protect themselves first, not you. If you’re using Google or Office 365 or Salesforce or Box or Dropbox or any of those platforms, there’s still a risk of data loss even though the data is in the cloud and there’s some protections on there.
We recommend the use of a third party backup system that the organization has control of. If there is a loss either due to intentional damage through a disgruntled employee, or accidental damage through a ransomware or crypto attack, you’re able to recover that data from a different system.
These may seem like basics, but making sure your operating system is up to date and making sure your third party applications are up to date as well. Microsoft has really forced this issue in terms of making updates a lot harder to ignore with Windows 10, but it’s also in response to the very real security risks that exist with running out-of-date operating systems and out-of-date applications.
We also see antivirus listed here that’s considered a core control. It’s not 100 percent effective. We do see quite a few Malware style attacks; I think less than it has been over time. I think we’re in a lull in traditional Malware that antivirus can protect against. It’s still an important piece to have deployed across your systems. And I think it’s important to be able to have it not only deployed, but also verified. So again, we deploy antivirus. We spend a lot of time and energy making sure that the systems are up to date. It’s active. It’s getting the most recent definitions. Because if it’s just deployed, but not up to date, then it’s not providing as much protection as it can.
And then, the next two controls here we see really focus on protecting against email based threats. From the graph before, we see that spam messages and business email compromise messages are the top two threats that we see coming into our helpdesk.
Spam is mostly annoying, but potentially has some malicious elements in it, in terms of maybe malicious attachments.
I think the real threat that causes real damage is around business email compromise, also potentially spear phishing where messages will try to get you to take some action. There may not be anything explicitly malicious in the message. There may just be a link to a website. The website isn’t holding Malware or going to run a virus on your computer, but it’s going to steal your credentials. It’s going to ask you to put in your password, so that you can get access to a file that your boss sent you or it’s going to invite you to fill out a form from a partner that you work with.
Being able to protect against those threats is really important to lower the stress that we see from staff. I mean, everybody can ignore the generic spam, the Viagra ads and all of that junk, it’s easy to ignore. It’s a lot harder for people to ignore that email that looks like it’s coming from their supervisor or looks like it’s coming from the boss to ask them to do something. It’s important to implement a specific control to block those types of threats.
And then, finally I wanted to highlight website protection. This would be for your organization’s website properties. I must say, I was surprised by the number of folks in the survey for the webinar who, when we asked, “Have you experienced any cyber security incidents?” How many people had said “Oh, yeah; our website was compromised.” I would say there were maybe 10 or 15 respondents saying their website was hacked.
I think that just shows the need to have protections. Just because you’ve got your website hosted with a vendor doesn’t mean that the website itself is being updated or it’s being protected against these kinds of ongoing malicious attacks.
So implementing some basic security controls around your website to make sure that if you’re using a popular CMS like WordPress, that the plugins are being updated, the system itself is being updated. Potentially adding in some additional web controls through vendors like CloudFlare who can help filter some traffic and provide an additional layer of protection is an important foundational piece.
I think there’s a lot of stuff in here. And I feel like I’ve moved more technology controls into “foundational” over time, because I think we’ve really seen the impact that they can have to an organization if they’re not there.
Proactive
So, now we get to move into a little bit of what I would consider more of the proactive section.
If you’re with me so far and you said, “Hey great, done! I checked all those things off the box,” that’s great. I’m really glad to hear it.
So now we’ll talk about some of the controls that are important to focus on once you get the basics done. This would be on the policy side and maybe the organizational assessment side would be the risk assessment piece. If you’ve got all the foundational controls underway that’s great. It’s probably a good opportunity to take a more formal look at the risks that you face as an organization. Maybe look at the types of adversaries your organization has, if any, the type of risks you face from the partners that you use. Just go through your systems to identify what may be at risk, what the impact could be, so that you can make an informed decision around which technology investments to make to protect those systems.
In this category, it’s also worth looking into a cyber liability insurance policy. It’s very unlikely that if you’ve not explicitly purchased cyber liability insurance that your current insurance coverage is going to protect you against things like ransomware or data breaches or any of that. It’s important for organizations to pursue and purchase coverage that’s going to address that specifically. And I would say, this is an area where we’re also seeing a lot of change. When I first started talking about cyber liability insurance, it was a very basic application. It basically didn’t matter what you put into it, but you could get coverage. Now, that’s really changed even this year where the applications have gotten a lot longer and how you are able to respond.
So again, have you implemented a multi-factor authentication, do you have an incident response plan, do you have data encryption in place? Those all have a meaningful impact in terms of whether you’ll get a policy or how much it’ll cost.
Guidance that I was giving a year or so ago, which was like “Hey, it doesn’t matter what you answer, they’re just writing policies,” I think is starting to shift. As we saw from the very early slides, the amount of cyber crime that is occurring with real financial impact continues to go up and so the cost to ensure all of those losses is going up as well.
Organizations are going to actually be compelled to make some of those changes, because insurance coverage is going to demand it. I’d be curious to hear from folks if that’s been their experience as well, in terms of having a more difficult time with their cyber liability insurance renewals or just even purchasing insurance in the first place.
And then, the final note we have here in the policy section is really around BYOD. Nonprofit organizations have really enjoyed flexibility with access to information and we’ve treated it as a benefit. “Hey, it’s great I can access my organizational email from my personal computer, there’s not all these hoops that we have to jump through.” But information is open and accessible. I think that’s also going to start to become an issue as well, as the risk of that approach becomes more clear.
As more and more data gets moved into the cloud, it’s easier to access. We don’t have this walled garden if you’re in the office or on a work computer, that’s the only way you can access the data. Now we’re shifting to working from home, working from the coffee shop. You can access all the organizational information.
What happens whenever you off-board an employee and all their data, all your organization data is synced to their personal computer? What remediation do you have to protect that, to retract that data to make sure that it doesn’t leave?
That starts with policy to govern that. Write down: are folks allowed to use personal devices to access information? If they do, are you providing a stipend for that? There’s a lot of elements that can go into the BYOD Policy and I think it’s an important step to take.
I think most organizations up until this point have really been, again, out of sight out of mind. It hasn’t been addressed and I think that’s starting to change.
As we move into the security awareness element, I think here’s where we really see the implementation of a formal learning management system to govern training. Shifting from “Hey, here’s some training. It’s available in the employee handbook,” or “Here’s some static resources that we’re going to make available that you can do on your own,” transitioning into a formal learning management system where you can prescribe certain courses; you can track employees progress; you can identify folks that maybe need some additional training or additional resources, you can test them.
We use Knowbe4 for security awareness training. It also does test phishing, which is really great. So we can test; we test our staff. Who’s clicking on these phishing messages that are getting through? What does it look like, the same thing happens for organizations. And we see really dramatic improvements again, we’ll do test phishing, we’ll provide some training, and we can really see the rate where staff are clicking on emails that they shouldn’t drops significantly.
We’re also seeing that these learning management tools like Knowbe4 are really expanding their use and adoption. They are providing cybersecurity training first and foremost, but then they’ve also added in elements of how they handle personally identifiable information, there’s some GDPR training elements that are included in the platform that we have access to, there’s HIPAA compliance training that gets included. It’s available in multiple languages.
It’s a really broad platform but I think more and more organizations are able to use and to plug in to provide meaningful training resources to their staff to raise the level of their education and awareness.
Proactive Technology Controls
The list of proactive controls on the technology side is still long. There’s lots of things to do here as well.
Specifically, single sign on, a password manager, this may get in a little bit of the technical weeds. With a password manager, you’re copying and pasting a username and a different password into every single site that you’re accessing.
Single sign on basically combines all of that and allows you to use one identity to access multiple systems. It uses some technologies called SAML or OAuth as a way to provide that authentication. The benefit there is that if you are able to integrate your organization’s systems into a single sign on, you’re able to easily off-board people. At many organizations, you’ve got 10, 15, 20 different cloud systems that you’re providing access to, so whenever you off-board somebody, you also have to take access away from 20 different systems and have to remember to do it.
With single sign on you have a single egress point into your network, and so you can just deactivate their work identity and then all the access to those other systems goes away as well. Super helpful technology as a way to provide better auditing and accountability for access to corporate systems.
Also wanted to raise in here some different data management or data governance controls, Microsoft would call that DLP, so if you’re in Office 365 there’s a really rich set of data loss prevention modules that are available within the SharePoint platform that can help you identify and block or take action on locations where you may have sensitive data like Social Security numbers, credit card numbers.
If you’re an organization it has to give HIPAA Compliance, there are HIPAA focused security controls that are available through the DLP engine formalizing some of those compliance requirements and then using the technology controls to help support them.
I’ve included BIOS and driver updates as a proactive control. That also may seem like a throwback, but it’s interesting. I was reading a note from Bret Arsenault who is the CISO for Microsoft. They just put out a survey that said over 80 percent of organizations have experienced firmware based attacks in the last two years, and identifying device firmware as an area that’s really been exploited.
Firmware is an underlying system that helps the computer operate. Several years ago, we actually upgraded our centralized management system to be able to automatically update the BIOS information for Dell computers specifically in reaction to the malware that targeted BIOS as a way to exploit systems. These systems are out there and available, but it takes some intentionality to do.
Updating BIOS, updating drivers, which can be exploited as well, requires some more sophisticated technology to make it happen. But it is available, and it’s clear that this is an area that Microsoft is seeing some increase in terms of the attacks in this area.
Talking about BYOD control, so you see we had policy in the last slide, now complemented with some technology controls as well. We can ensure that if we say, “By policy, only work computers can access organizational data,” you can implement some additional controls to provide technical validation and verification, but that is indeed true. So, if the organization computer needs to be joined to Azure active directory, it needs to be compliant. It needs to be encrypted and then it can access the data. If it doesn’t meet those categories, then it can’t access the data. BYOD control is the technology implementation of the policy work that you did already.
Endpoint detection and response is an evolution or Next-Gen AV it’s sometimes also referred to, AV relies typically on a more static analysis. Here’s this fire signature, we’re going to compare files to see if they match known signatures and if they do, we’re going to block it.
Endpoint detection and response is really an evolution of that. Tools will be able to identify known malware but then they’ll also be able to look for PowerShell scripts that are doing things that are unexpected or unique antivirus. And so it’s able to do analysis of systems based on behavior, not just static signature analysis. These tools are a little bit more expensive but provide a lot more value. They often can be integrated into other security systems and provide more detailed and rich logging history, so that you can go and track down what applications the user may have accessed or what systems processes are running on a computer at a certain time.
A really rich set of features are available through these endpoint detection and response systems. The vendors that you’ll see in this space are going to be ones like SentinelOne, and CrowdStrike, which are ones we’ve used. Carbon Black, there’s a whole cottage industry in this sector because it’s a very hot space, and really does provide a lot of value.
And then the final technology control here is around web filtering, so this would be on personal computers or organization computers getting access to the web. We know that the number of viruses that are delivered through email is actually relatively low, but we are seeing lots of malicious content that’s attempted to be launched through websites or malformed websites themselves.
Having a tool in place that can do what’s called some type of DNS filtering so that they can block known malicious sites is really a helpful layer of protection. You can prevent the computers from even going to malicious sites in the first place. Sites that may be running cryptojacking software or some kind of malicious advertising that’s going to inject into an unpatched browser for example.
We use Cisco Umbrella. Cloudflare has a web browsing or a DNS filter tool. There’s a lot of tools out there that are able to provide this protection, and as a long time customer, it’s been a really effective piece of our overall control that we include as part of our device management to make sure the devices that we support are really secured and protected from a layer of different technologies.
Optimized
To move into the optimized section: maybe fewer controls here, but maybe more sophisticated. By this point, an organization is probably ready for a formal business continuity plan.
For many organizations, this past year has been a living example of what you’re actually doing, so it may be good to write it down. I would say that business continuity planning is not an exercise for the IT staff to take on, that’s something that’s typically led from the executive layer at the organization. I know at Community IT, our CFO led our business continuity planning.
I provided input that’s part of the technology perspective, but this is really a focus around the operations of the business. As such, it takes a bit more time, a bit more focus, a broader focus for the organization to implement. Business continuity planning I would expect to see at this level.
And then security awareness. It’s also probably time for a much more formalized external assessment to help the organization really identify, rank and prioritize the technology investments that need to be made moving forward. A really detailed evaluation of the controls that are in place, that could be put in place, for the organization to be able to check off all the boxes they need to really ensure that their cybersecurity controls and protections are working for them.
We see a lot of technology controls in here as well, and these tend to be a little bit more expensive. We’ve got the concept of Device Trust or Zero Trust, there’s a lot of different ways that this gets talked about.
Most of us are familiar with the model of: you want to access Office 365, you open up your web browser, you go to Office 365, you get access, you put in your username and password, no problem.
Device trust or zero trust would turn that on its head a little bit. So instead of any website being accessible from anywhere from any device, access is only granted to trusted devices with known identities that have compliant software on their computer. There’s a lot more control that gets exerted over access to systems.
It really reduces the surface area of your attack. It’s kind of jargon, but it’s a much more focused way to provide access.
From the cyber ops side, the incident hunting side, one of the challenges that we face with working from home is now we’re seeing IP address connections come from all over the place. Whereas before we could clearly say, this person is working in the office, great; that’s a known good connection.
Now, people are working all over the place, they’re using VPN connections and so it’s much, much harder to troubleshoot and to identify potentially malicious connections. It’s also a lot more difficult to secure, because we’re not able to say, hey we’re only going to allow access from X, Y or Z location. It needs to be a lot more broad in terms of access and how access is given.
So you can kind of flip that on its head and say, “We’re only going to allow access to our systems from trusted devices.” Then you really narrow your surface area.
And that leads into the next line item here, which is a bunch of acronyms for CASB and SASE. Everybody loves those acronyms.
It sounds like a bunch of marketing mumbo jumbo, but these are real and meaningful technology controls that we’re starting to see more clients explore and implement. CASB stands for Cloud Access Services Broker, and then SASE is Secure Access Service Edge. These are ways to provide managed egress points for access into your network.
As many, many things are now purely cloud, these tools would say they’re able to validate the devices and users, provide access to a list of managed applications, report audit and provide governance information around those applications and potentially other security controls around that.
They provide some comprehensive security. Microsoft includes some elements of this within their platform, Cloudflare has also provided some access to this as part of their platform. There’s dedicated vendors that do this. This is a burgeoning area and more and more organizations are going to take advantage of it as a way to secure and manage and provide access to their cloud applications.
Potentially a new entry into our list of optimized technology controls and something that’s worth taking a look at if you’ve been able to do some of the other things as prerequisites.
We also have vulnerability scanning and penetration testing here as additional technology controls. Once you’ve been able to focus on all those other things: your devices are updated, they’re secured, you’re doing patching, you’ve got your security tools in place, then it’s worth investing in some of these additional vulnerability scanning systems so that they can scan to detect where you may have gaps.
This may be appropriate to larger organizations that still have some on-prem server infrastructure. I think we’re starting to see some additional tools become available for looking at access to cloud systems to see what gaps there might be in terms of governance and compliance or access issues that those applications may have. But vulnerability scanning and penetration testing, as well.
Penetration testing, it tends to be very expensive because you’re enlisting the help of highly skilled and highly trained security testers that are going to attack your organization as if they were a malicious adversary. They will maybe use some automated tools, they may use some additional tools and techniques to attempt to infiltrate your organization, your network, and then develop a detailed list of recommendations and improvements for how to secure the organization.
Some organizations may be required to do these, and if you are, you’ve got your path set up for you. I would say this would be one of the last things I would suggest doing for an organization. Make sure you’ve got all your other security controls in place before you invest in a penetration testing engagement.
And then the final tool here listed would be a SOC or Security Operation Center or SIEM, Security Information Event Center, these are really tools and platforms that take all of that event information that we’ve been talking about. From your single sign-on solution, maybe from your device management solution, from your endpoint detection response solution, and suck it all up into one data platform.
Then you can analyze and correlate data across multiple different platforms. The examples are given and you would be able to see an email come through your filter, land in somebody’s inbox, see who opened it, see who else that email went to, was it malicious, and be able to track down and provide reporting.
So again this may be a control that you’re required to have, if you have data retention requirements or logging retention requirements. This is the way that you would be able to do and meet those compliance requirements.
It’s a lot of different things here in terms of the technology and policy and training elements that are available for organizations to follow.
Getting Started
I wanted to also mention getting started. There is a lot of data that we talked about, a lot of different things you could do. And I wanted to say that there’s no one right way to do things. I think we’ve seen organizations be successful in many different ways.
They’ve been successful from a bottom-up approach, somebody in IT really takes ownership and leads the process. We’ve also seen top-down be effective in terms of executive leadership or maybe the board decides this is something that needs attention and it’s a top-down approach. There’s no one right way for an organization to get started with getting traction. The bottom line is somebody needs to decide that it’s important and then take action.
So if you’re looking at getting started, I would say that it’s important to
- Leverage your existing requirements. Maybe your organization already has some kind of formal compliance mandate that you need to meet, whether that be HIPAA, whether it be FERPA, whether it be organizations that have to deal with credit card information in any form you need to follow PCI compliance standards, that’s appropriate for them. There’s probably already a compliance standard that you’re supposed to be following. You can use that as a way to jump start this process if you feel like you’re not able to get traction.
- It’s important that the organization establish an IT working group. I don’t think this is something that just one person can take on at an organization. It probably needs to have multiple stakeholders as a way to provide some structure and accountability and broader perspective. It’s not something that IT is just going to come in and make everybody secure. That’s not how it’s going to work, IT needs to work with other departments in order to implement these controls effectively.
- I think it’s important to connect with a partner to execute on this. These are really specialized controls in some places. You don’t need to reinvent the wheel for yourself. there’s lots of skilled and talented partners that are out there that will help you navigate this and provide some tailored consulting and solutions that’ll work for you, so that you can leverage their experience and not need to try to build it all up yourself.
If you can find a partner that’s going to be a good companion, not somebody that’s just going to drop in some solutions and then walk away. It’s important that there is education, engagement awareness, so that you understand what’s being recommended, what’s being implemented and then how it’s being carried out.
- And then finally, if you’re large enough, or you’re able to, having board engagement is really important. If you have a board, it’s likely they already have a governance committee. This is something that may fall under their purview. Engaging with the board and some way to connect up the ladder to make these meaningful changes is really important. I would encourage that.
Let’s Talk
Now, we’re running out of time, I did want to highlight here: I’m happy to have a conversation; if you have questions you can get in touch on our Cybersecurity page.
You could also book some time with me directly. That’s my meeting link, and Johan, if you want to put that in the chat, that’s great. I’m happy to have a conversation and answer your questions you may have about how you can get started with cybersecurity at your organization.
I’ll actually be back next month along with our colleague Peter Mirus at Build Consulting to talk about cyber security specifically and about budgeting for that. So we’ll probably take some of this information and talk a little bit about putting this all into action in terms of budget and budget development for this.
Johan, were there any comments or questions that I didn’t get to you or required a little bit of follow-up?
Johan Hammerstrom: I don’t think so. It was very thorough, thank you Matt. I always enjoy these webinars. I’m constantly learning about cybersecurity.
It’s something I’m interested in, but also is vital for us as a managed services provider, and these webinars are always really very helpful and informative. There were a few questions I was able to answer along the way and no outstanding questions at this time, but I would encourage everyone to take advantage of Matt’s offer to meet up and you can schedule time with him.
You can reach out to us through our Cybersecurity page and if you had a security question that you weren’t ready to ask, that’s fine. We are here. So thank you everyone for joining us today, thank you again Matt, for your time and for all the great information you shared with us and we look forward to seeing everybody next month.
Matthew Eshelman: All right, great. Thanks so much.
Johan Hammerstrom: Take care. Thanks so much for attending. Community IT does these free webinars for our community, and we love sharing our knowledge and experience. If you have more questions or are having trouble with your IT at your non-profit, please get in touch with us on our website wwwcommunityit.com. So we can start a conversation or schedule an assessment. Downloading any of our free resources there will get you signed up for our webinar reminders and you could attend our next webinar in real time and ask our experts your own questions.
Never miss a new video by subscribing here on YouTube.